WordPress vulnerabilities and how to overcome them with Sectigo Web Security

WordPress is no stranger to many of us and there is a very good reason behind it. Why? That is because it is the world’s most popular Content Management System (CMS), used by numerous websites big and small. In fact, according to BuiltWith®, nearly 37% of the top 1 million websites in the world use WordPress as of the time of writing. On the entire Internet, it is a solid 43% out of nearly 65.5 million websites that are using WordPress.
With such an enormous usage distribution in the Internet world, it is only natural that WordPress has become the favourite target for hackers and cybercriminals to exploit its vulnerabilities. These notorious cyber attackers are constantly on the lookout for any exploitation opportunities in WordPress vulnerabilities, even going as far as using automated programmes to hunt for their next victim who is a WordPress user in order to launch their attacks at the fastest possible.
How do cyber attackers find exploitation opportunities in WordPress websites?
As with any software in the digital landscape, WordPress is also prone to code defects and flaws in the way it is designed and coded, or even due to technology advancement which causes some codes to no longer work as intended. The community of dedicated developers behind WordPress are constantly improving its codes. Hence, websites which use WordPress will usually become outdated in its codes, system files or even architecture frequently, because the developers are working hard and pushing many new fixes and updates from time to time.
 WordPress websites running on outdated codes and system files present security loopholes and weaknesses, which are great exploitation opportunities for cyber attackers. These websites usually share some common security vulnerabilities which are exploited by cyber attackers. They use these vulnerabilities to take control of WordPress websites in executing various cyberattacks, steal data that they can use or sell, spread malware, bypass authentication mechanisms, make unauthorized website changes and transactions, or even taking down websites to demand ransoms. Continue reading below to see these common WordPress security vulnerabilities.
WordPress websites running on outdated codes and system files present security loopholes and weaknesses, which are great exploitation opportunities for cyber attackers. These websites usually share some common security vulnerabilities which are exploited by cyber attackers. They use these vulnerabilities to take control of WordPress websites in executing various cyberattacks, steal data that they can use or sell, spread malware, bypass authentication mechanisms, make unauthorized website changes and transactions, or even taking down websites to demand ransoms. Continue reading below to see these common WordPress security vulnerabilities.
Common WordPress security vulnerabilities and what to do about them
The following list presents you with a general idea of the common WordPress security vulnerabilities that cyber attackers tend to target when they are looking to exploit a WordPress website. Keep in mind that this is not a definitive list, and there are other approaches that they can use.
Vulnerability 1: Login Fields
WordPress allows for users to login to an admin dashboard to manage their website. The login page fields are vulnerable to attacks as cyber attackers have tools to bypass the authentication management. One such popular method used by them is brute force attack, where they use automated bots to continually input login credentials to the login fields until it is successful in finding the right password. Once they get access to a WordPress website through an unprotected login field, they can use it to perform illegal activities.
Recommended solutions for this vulnerability
WordPress website owners are recommended to enforce these methods in order to protect their login fields.
Firstly, limit the login attempts a user can attempt in a set period. Once the user reaches the maximum number of attempts, his/her IP address will be blocked and he/she cannot try to login anymore.
Secondly, enforce using strong passwords for users who have access to the admin dashboard. The key thing about a strong password is that the longer it is the better, as well as it is alphanumeric: a mix of letters (upper and lower case), numbers, and symbols, with no ties to personal information and no dictionary words.
Thirdly, implementing two-factor authentication (2FA) adds an extra layer to the login procedure, which ensures extra safety by requiring users to submit a unique number/pin that is sent to their phone or email.
Last but not least, change the login username into something unique. Generic and common terms like “Admin”, “User” are easy to exploit using brute force attack.
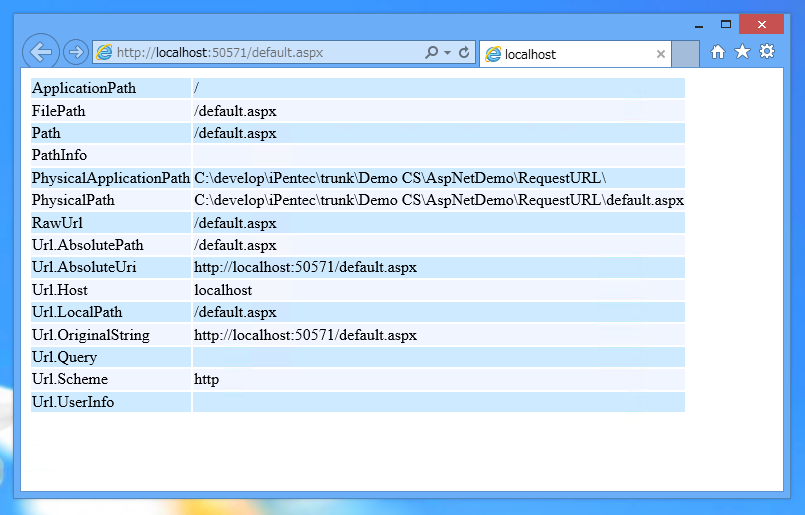
Vulnerability 2: Default URL and File Names
When a WordPress website is setup initially, the system uses default URLs, file names and storage locations to prepare the resources. These are important pages and hackers know about this, which makes it easier for them to launch brute force attacks if the website owners do not manually change them.
Recommended solutions for this vulnerability
Firstly, make sure to change the default URL path for admin page. WordPress uses the following URLs as the default admin page links: “www.yourdomain.com/wp-login.php” and “www.yourdomain.com/wp-admin”. Anyone on the Internet including hackers can easily reach this page. Therefore, it is recommended to be creative and change the admin page URL to something else that is more unique.
Secondly, make sure to change the default database table name which uses wp- prefix. Important data such as login credentials, user info, transaction details and much more are stored in these tables. Hackers are aware of this and targeting database to extract this important data is a common approach for them. Therefore, it is recommended to change the prefix to something unique.
Thirdly, make sure to change the location of the wp-config.php file. This file is the backbone of a WordPress website’s settings, configurations, authentication keys and database. Hackers love to target this file, because it gives them a lot of info about the website. Move the wp-config.php file to any other folder above the root directory that’s not a subdirectory of your public_html or WWW folder.
Vulnerability 3: Absence of data transmission encryption
The absence of data transmission encryption means that when data is exchanged and transmitted insecurely between a user’s browser and a web server, it is transmitted in plain text. Cyber attackers can intercept the transmission and extract the data. They use the man-in-the-middle attack approach to do so, which allows them to get hold of the sensitive data (name, email address, password, payment card details, tax-related information, etc.). They can in turn use this data to commit crimes like identity theft, fraud, blackmailing or ransoming.

Recommended solution for this vulnerability
It is extremely important to address this vulnerability by installing SSL/TLS certificates on the WordPress website. Why so? Click here to read the importance of SSL certificates for websites. Doing so will help WordPress website owners to encrypt data transmission between a user’s browser and their web server, which then removes a vulnerability that cyber attackers can take advantage of.
Vulnerability 4: Lack of web security tools like firewalls, malware/vulnerability scanners
Many WordPress websites do not have web security tools installed to continuously monitor for cyberattacks, malware or vulnerabilities. This presents an opportunity for cybercriminals to attack the websites from behind the shadows, such as secretly inserting malicious codes or files without the website owners knowing. By the time the cyberattacks are discovered, it was too late.
Recommended solution for this vulnerability
Implement cybersecurity solutions and tools to solve this vulnerability. Install WordPress security scanners and firewalls to monitor the WordPress website 24/7 for enhanced protection. We recommend Sectigo Web Security, a modern, comprehensive and automated web security solution and tool. It scans the website daily and monitor for any changes in code and files and immediately notifies the website owner about it.
Vulnerability 5: Outdated WordPress components, files, plugins, themes
As mentioned earlier, WordPress is continuously improving and updating. As such, its powerful features and components such as files, plugins and themes need to be frequently updated as well, in order to ensure compatibility and that they are working properly. However, many WordPress website owners tend to be slower in installing updates, and hence their websites still run on outdated versions. Cybercriminals take advantage of this to exploit security loopholes and weaknesses in old versions.

Recommended solution for this vulnerability
Firstly, it is recommended to always install plugins and themes developed by trusted and reliable developers. They are better because they are actively maintained and updated to keep up with the changes of WordPress. Hence, they are less likely to have vulnerabilities to be exploited by cybercriminals.
Last but not least, always update WordPress versions whenever there is a new one. This reduces the likelihood of security loopholes and weaknesses that can be exploited by cyber attackers.
Vulnerability 6: Unprotected input fields
WordPress websites almost always have a variety of input fields including contact and subscription forms, login fields, comments, or a search bar. These input fields are vulnerable in that cyber attackers can insert malicious codes or scripts to execute cross-site scripting (XSS) or SQL injections. Some attackers even insert unwelcome ads or malicious links in the comments section to trick users.
In XSS attacks, hackers insert scripts in any vulnerable input fields. When users click them, they unknowingly download the malware in their computers, they are redirected to a dangerous website, or the data they have provided is stolen by the hackers.
In SQL injection attacks, hackers write malicious code and try to insert them to the system via web application input fields and form input fields. If inserted successfully, they gain access to the core system files without needing to go through the websites’ authentication process. This will allow them to extract sensitive data, or even hijack entire databases via ransomware attacks.
Recommended solutions for this vulnerability
Having input fields are inevitable in most websites, but there are a few recommended solutions. Firstly, limit and minimise user inputs. Less inputs mean lower risks of attacks. Secondly, make sure to validate and whitelist data. Make sure the input fields only accept the required data formats. Thirdly, take it further by sanitising inputs following the second step. Scan all the input data and remove malicious codes before allowing it to enter the database. Next, make sure to block spammy contents in the comments sections. In addition, regularly update the WordPress website and all of its core components. Finally, make sure to use web application firewalls or any other protection tools to protect the website at all times. We recommend using Sectigo Web Security to do this.
Protect your customers’ WordPress websites with Sectigo Web Security
WebNIC is an official partner of Sectigo in promoting and selling Sectigo Web Security services. We have prepared in place the necessary tools, marketing materials and help you might require to start selling! It is a comprehensive, modern and convenient web security solution, which comes with powerful web security features, including Web Detect, Web Patch, Web Clean, Web Backup & Restore, Web Accelerate, Web Firewall and Web Comply. With it, web security service selling is now made easy for you! Protecting WordPress websites is no longer a challenging service to offer to your clients. Join WebNIC as a partner and start selling it today!


About WebNIC
WebNIC operates a digital reseller platform covering primarily domain name registration for over 600 TLDs, web security services, email and cloud services. With offices in Singapore, Kuala Lumpur, Beijing, Taipei and Jakarta, we serve 5,000 active resellers in over 70 countries. With over 20 years’ experience, we accelerate our partner’s growth through a robust platform, attentive support and wholesale pricing. To join us and become a reseller, live chat with us or email us at inquiry@info.webnic.cc.